Have you ever needed to collect an additional piece of information, not collected by LANDESK by default, from one of your managed Macs? The answer to that question will very likely be yes simply because every business environment is unique.
Often, the additional information that needs to be collected is simply a matter of enabling the LANDESK inventory scanner to pickup a new file type. These types of changes are easy and can be added by leveraging the Manage Software List tool within the LANDESK console. For more information on this method, see the LANDESK 9.6 Help file link.
However, if you want to collect the state of an object on the device, it may require a script to be written to query OS X itself. The response from the OS will then need to be captured in a format the LANDESK inventory scanner can then pick up and transmit back.
By default, the LANDESK inventory scanner can parse an XML or PLIST file placed in the “/Library/Application Support/LANDesk/CustomData” directory. As such, we just need to write a script that places the response from the OS query into an XML or PLIST file and save it to the CustomData folder. So doing will allow you to collect any type of information that may be relevant in your environment
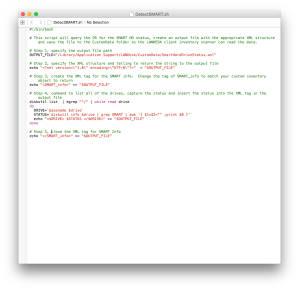
The script below, written by Steve Goodrich for a LANDESK Interchange session, is an example script in which the OS is queried for the S.M.A.R.T. status after which the result is written to an output XML file.
This article will walk through each step of the script to explain what is going on, however, it will not be covering the details of XML and BASH. I’ve posted some links below to research additional information on XML or BASH.
XML
Bash Scripting
- http://www.tldp.org/LDP/Bash-Beginners-Guide/html/
- http://www.tldp.org/LDP/abs/html/
- http://tldp.org/HOWTO/Bash-Prog-Intro-HOWTO.html
OK, let’s create our script. The first thing we need to do is open an editor. On OS X, I prefer to use Xcode. However there are a number of editors out there, like TextWrangler. Just choose one that fits your preference. The first line in the script needs to specify it’ll be using BASH. As such, write:
#! bin/bash
Now we need to specify the output file variable that’ll be called throughout the script along with it’s associated file path. Because we want the LANDESK inventory scanner to pick up the information, we’ll write out output file to the CustomData folder and give it a name of SmartHardDriveStatus.xml. You can name your file whatever makes sense for the information you’re collecting.
OUTPUT_FILE="/Library/Application Support/LANDesk/CustomData/SmartHardDriveStatus.xml"
Next we’ll specify inside the output file, the XML structure we’ll be creating. The echo command will place the text after the quotes into our XML file. The carrot “>” before the “$OUTPUT_FILE” is telling the echo command where to write and the “$OUTPUT_FILE” is referring the variable created previously.
echo "<?xml version=\"1.0\" encoding=\"UTF-8\"?>" > "$OUTPUT_FILE"
With the output file created and the XML structure specified, we need to create the opening XML tag in which we’ll save the SMART status inside of.
echo "<SMART_info>" >> "$OUTPUT_FILE"
OK, now we’re to the fun part. We need to query OS X and obtain the status of the hard drive. This can be accomplished using the diskutil command. Most likely, the custom information you want to obtain will require a different command to query the OS. Use the internet to search for the command you need and replace it with what is below. Just make sure you echo your result and write it to an XML tag. The example below has the results from the variables DRIVE and STATUS being written to an XML tag named from the DRIVE variable with the STATUS being written as the information inside the XML tag.
diskutil list | egrep "^/" | while read drive
do
DRIVE=`basename $drive`
STATUS=`diskutil info $drive | grep SMART | awk '{ $1=$2="" ;print $0 }'`
echo "<$DRIVE> $STATUS " >> "$OUTPUT_FILE"
done
The final step to the script requires us to close out the first SMART_info tag we created. It’s a pretty simple command.
echo "</SMART_info>" >> “$OUTPUT_FILE"
That’s it. You can save your script as a .sh file. Completed, it’ll look similar to what I have below:
#!/bin/bash
# Create the Output file with the appropriate XML structure so the inventory scanner can read the data
# The output file path
OUTPUT_FILE="/Library/Application Support/LANDesk/CustomData/SmartHardDriveStatus.xml"
# specifying the XML structure and telling to return the string to the output file
echo "<?xml version=\"1.0\" encoding=\"UTF-8\"?>" > "$OUTPUT_FILE"
# creating the XML tag for the SMART info. Change this to match your custom inventory
echo "<SMART_info>" >> "$OUTPUT_FILE"
# command to list all of the drives, capture the status and insert the status as XML output in the output file
diskutil list | egrep "^/" | while read drive
do
DRIVE=`basename $drive`
STATUS=`diskutil info $drive | grep SMART | awk '{ $1=$2="" ;print $0 }'`
echo "<$DRIVE> $STATUS </$DRIVE>" >> "$OUTPUT_FILE"
done
# close the XML tag for SMART Info
echo "</SMART_info>" >> "$OUTPUT_FILE"
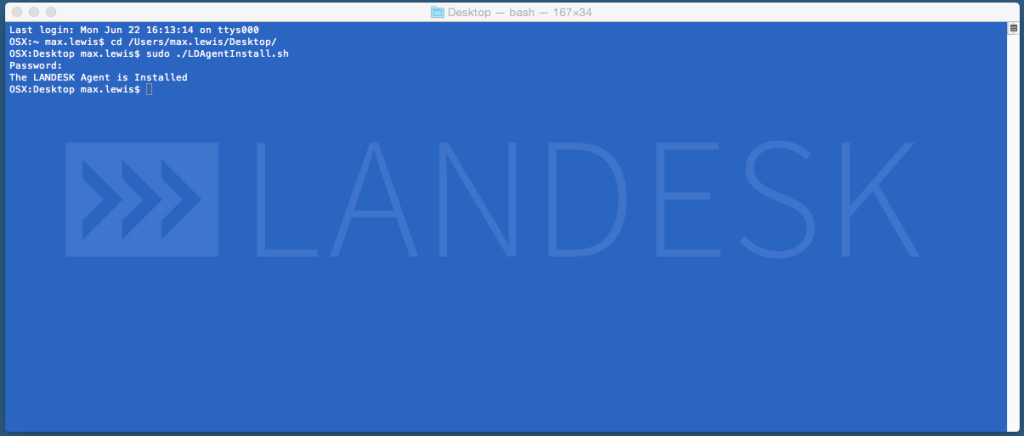
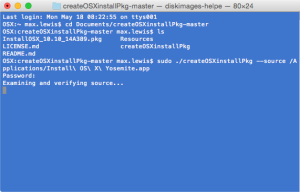
To test it out, modify the properties of the file to make it executable. To do this, you’ll need to open up Terminal and browse to the path of where the script has been saved. You’ll then need to run the command:
chmod a+x scriptfilename.sh
Once the executable properties have been given to the file, you can manually run it on your test machine by calling it in terminal.
sudo ./scriptfilename.sh
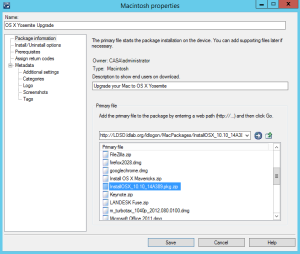
In my next post I’ll walk through how we can use the pkgbuild command to create a package out of our script, deploying it the Apple-esque way as opposed to the UNIX method of deploying a .sh file.










Recent Comments